Forensic radio surveying is undertaken in support of the digital forensics discipline of cell site analysis. The ability to demonstrate a full understanding of cellular technologies and forensic radio surveying techniques is vital if surveyors are called to court to explain their evidence. A lack of technical knowledge or understanding may be quickly discovered under cross-examination and will be used to undermine the credibility of any cell site evidence being presented. The aim of this course is to provide an understanding of forensic radio surveying for new entrants into this fascinating field and to act as an aide-memoire to remind more experienced forensic radio surveyors.
EXPECTED ACCOMPLISHMENTS
- Discuss the motivation for Mobile Forensics
- Step through a survey of mobile technologies from 2G to 5G
- Differentiate between cell site and cell phone forensics
- Conduct idle and connected mode forensic radio survey
- List types of evidence that can be extracted via cell phone forensics
- Identify the operating systems used by mobile phones
- Demonstrate an understanding of SW and HW tools used in mobile forensics
- Step through the mobile forensic investigation process
- Understanding the scientific method relating to mobile radio forensic radio survey
- Present results as factual evidence by producing detailed maps and reports for the court or an investigative team.
TARGET AUDIENCE
This course is suitable for information security professionals, risk assessment, law enforcement officers, and government agencies.
COURSE DETAILS
1. Introduction to Mobile Forensics
- Criminalistics and criminology
- Locards exchange principle
- Forensics sciences and expert testimony
- Cell phone forensics vs. computer forensics
- Case studies
- Complications of cell phone forensics
- Types of cell phone evidence
- Cell phone geometry
- Obtaining evidence from the operator
- Scientific method (pertaining to criminalistics)
- Legal procedures
- SV Probe directed graph of callers
2. Forensic Evidence
- Need for Faraday cage
- logic bombs
- jamming devices
- Usage logs/billing records
- Smartphone evidence
- SIM types
- Date and timestamps
- Remote wipe
- Third-party apps
- Dirty mobiles
- GPS metadata
- WiFI SSIDs
- SIM cloning
- Breadcrumbs geotagging
- Extraction of forensic evidence
- Seizing evidence
- Best practices
3. Mobile Networks
- GSM/GPRS/EDGE networks
- UMTS/HSPA networks
- LTE/LTE-A networks
- 5G Networks
- Traffic cases
- Mobile originated and terminated calls
- Handover
- Location updating
- Roaming
4. Cell Site Forensics
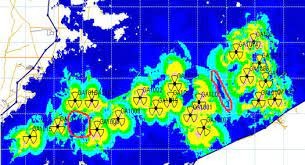
- Cell site analysis
- Call detail records
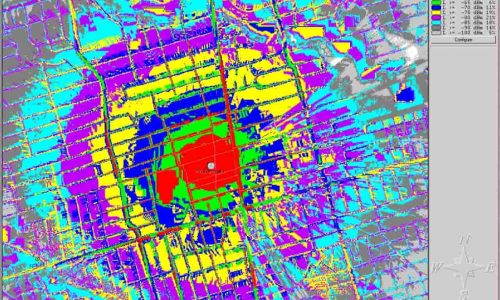
- Spot location survey
- Lawful Interception
5. Cell Phone Forensics
- What a criminal can do with a mobile phone
- Cell phone forensic challenges
- Forensic information in a mobile phone
- SIM and SIM file system
- IMSI, IMEI
- ICCID, ESN
- Precautions to be taken before investigation
- Securing files with hashing.
- Mobile phone HW characteristics
- Mobile phone SW characteristics
- Operating Systems
- Mobile forensic process
- Mobile forensic tools
- Cell Parameters